CAS-004 Online Practice Questions and Answers
Questions 4
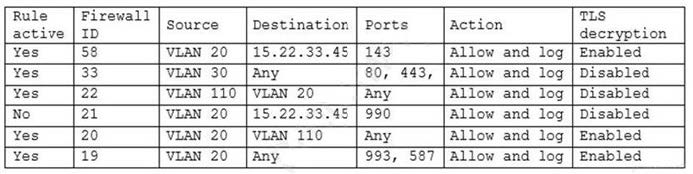
A security engineer has been asked to close all non-secure connections from the corporate network. The engineer is attempting to understand why the corporate UTM will not allow users to download email via IMAPS. The engineer formulates a theory and begins testing by creating the firewall ID 58, and users are able to download emails correctly by using IMAP instead. The network comprises three VLANs:
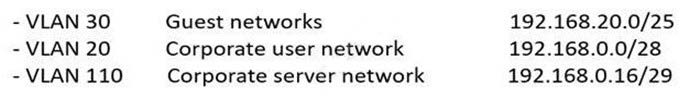
The security engineer looks at the UTM firewall rules and finds the following:
Which of the following should the security engineer do to ensure IMAPS functions properly on the corporate user network?
A. Contact the email service provider and ask if the company IP is blocked.
B. Confirm the email server certificate is installed on the corporate computers.
C. Make sure the UTM certificate is imported on the corporate computers.
D. Create an IMAPS firewall rule to ensure email is allowed.
Questions 5
After a security incident, a network security engineer discovers that a portion of the company's sensitive external traffic has been redirected through a secondary ISP that is not normally used. Which of the following would BEST secure the routes while allowing the network to function in the event of a single provider failure?
A. Disable BGP and implement a single static route for each internal network.
B. Implement a BGP route reflector.
C. Implement an inbound BGP prefix list.
D. Disable BGP and implement OSPF.
Questions 6
An organization recently started processing, transmitting, and storing its customers' credit card information. Within a week of doing so, the organization suffered a massive breach that resulted in the exposure of the customers' information. Which of the following provides the BEST guidance for protecting such information while it is at rest and in transit?
A. NIST
B. GDPR
C. PCI DSS
D. ISO
Questions 7
An enterprise is undergoing an audit to review change management activities when promoting code to production. The audit reveals the following:
1.
Some developers can directly publish code to the production environment.
2.
Static code reviews are performed adequately.
3.
Vulnerability scanning occurs on a regularly scheduled basis per policy.
Which of the following should be noted as a recommendation within the audit report?
A. Implement short maintenance windows.
B. Perform periodic account reviews.
C. Implement job rotation.
D. Improve separation of duties.
Questions 8
A company that uses AD is migrating services from LDAP to secure LDAP. During the pilot phase, services are not connecting properly to secure LDAP. Block is an except of output from the troubleshooting session:

Which of the following BEST explains why secure LDAP is not working? (Select TWO.)
A. The clients may not trust idapt by default.
B. The secure LDAP service is not started, so no connections can be made.
C. Danvills.com is under a DDoS-inator attack and cannot respond to OCSP requests.
D. Secure LDAP should be running on UDP rather than TCP.
E. The company is using the wrong port. It should be using port 389 for secure LDAP.
F. Secure LDAP does not support wildcard certificates.
G. The clients may not trust Chicago by default.
Questions 9
A server was compromised recently, and two unauthorized daemons were set up to listen for incoming connections. In addition, CPU cycles were being used by an additional unauthorized cron job. Which of the following would have prevented the breach if it was properly configured?
A. Set up log forwarding and utilize a SIEM for centralized management and alerting.
B. Use a patch management system to close the vulnerabilities in a shorter time frame.
C. Implement a NIDS/NIPS.
D. Deploy SELinux using the system baseline as the starting point.
E. Configure the host firewall to block unauthorized inbound connections.
Questions 10
A corporation with a BYOD policy is very concerned about issues that may arise from data ownership. The corporation is investigating a new MDM solution and has gathered the following requirements as part of the requirements-gathering phase.
1.
Each device must be issued a secure token of trust from the corporate PKI.
2.
All corporate application and local data must be able to deleted from a central console.
3.
Cloud storage and backup applications must be restricted from the device.
4.
Devices must be on the latest OS version within three weeks of an OS release.
Which of the following should be feature in the new MDM solution to meet these requirement? (Select TWO.)
A. Application-based containerization
B. Enforced full-device encryption
C. Mandatory acceptance of SCEP system
D. Side-loaded application prevention
E. Biometric requirement to unlock device
F. Over-the-air restriction
Questions 11
A network administrator receives a ticket regarding an error from a remote worker who is trying to reboot a laptop. The laptop has not yet loaded the operating system, and the user is unable to continue the boot process. The administrator is able to provide the user with a recovery PIN, and the user is able to reboot the system and access the device as needed. Which of the following is the MOST likely cause of the error?
A. Lockout of privileged access account
B. Duration of the BitLocker lockout period
C. Failure of the Kerberos time drift sync
D. Failure of TPM authentication
Questions 12
Which of the following is a security concern for DNP3?
A. Free-form messages require support.
B. Available function codes are not standardized.
C. Authentication is not allocated.
D. It is an open source protocol.
Questions 13
IoCs were missed during a recent security incident due to the reliance on a signature-based detection platform. A security engineer must recommend a solution that can be implemented to address this shortcoming. Which of the following would be the most appropriate recommendation?
A. FIM
B. SASE
C. UEBA
D. CSPM
E. EAP
