XK0-005 Online Practice Questions and Answers
Questions 4
A systems administrator received a notification that a system is performing slowly. When running the top command, the systems administrator can see the following values:
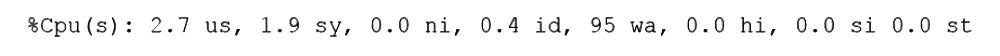
Which of the following commands will the administrator most likely run NEXT?
A. vmstat
B. strace
C. htop
D. lsof
Questions 5
A non-privileged user is attempting to use commands that require elevated account permissions, but the commands are not successful. Which of the following most likely needs to be updated?
A. /etc/passwd
B. /etc/shadow
C. /etc/sudoers
D. /etc/bashrc
Questions 6
A junior administrator is trying to set up a passwordless SSH connection to one of the servers. The administrator follows the instructions and puts the key in the authorized_key file at the server, but the administrator is still asked to provide a password during the connection.
Given the following output:
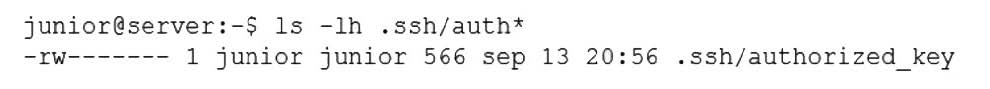
Which of the following commands would resolve the issue and allow an SSH connection to be established without a password?
A. restorecon -rv .ssh/authorized_key
B. mv .ssh/authorized_key .ssh/authorized_keys
C. systemct1 restart sshd.service
D. chmod 600 mv .ssh/authorized_key
Questions 7
Users in the human resources department are trying to access files in a newly created directory. Which of the following commands will allow the users access to the files?
A. chattr
B. chgrp
C. chage
D. chcon
Questions 8
Due to low disk space, a Linux administrator finding and removing all log files that were modified more than 180 days ago. Which of the following commands will accomplish this task?
A. find /var/log -type d -mtime +180 -print -exec rm {} \;
B. find /var/log -type f -modified +180 -rm
C. find /var/log -type f -mtime +180 -exec rm {} \
D. find /var/log -type c -atime +180 璻emove
Questions 9
Which of the following technologies provides load balancing, encryption, and observability in containerized environments?
A. Virtual private network
B. Sidecar pod
C. Overlay network
D. Service mesh
Questions 10
A DevOps engineer is working on a local copy of a Git repository. The engineer would like to switch from the main branch to the staging branch but notices the staging branch does not exist. Which of the following Git commands should the engineer use to perform this task?
A. git branch --m staging
B. git commit --m staging
C. git status --b staging
D. git checkout --b staging
Questions 11
A Linux administrator needs to resolve a service that has failed to start. The administrator runs the following command:
The following output is returned
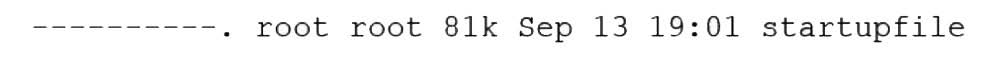
Which of the following is MOST likely the issue?
A. The service does not have permissions to read write the startupfile.
B. The service startupfile size cannot be 81k.
C. The service startupfile cannot be owned by root.
D. The service startupfile should not be owned by the root group.
Questions 12
A cloud engineer wants to delete all unused networks that are not referenced by any container. Which of the following commands will achieve this goal?
A. docker network erase
B. docker network clear
C. docker network prune
D. docker network rm
Questions 13
A systems administrator created a web server for the company and is required to add a tag for the API so end users can connect. Which of the following would the administrator do to complete this requirement?
A. hostnamectl status --no-ask-password
B. hostnamectl set-hostname "$(perl -le "print" "A" x 86)"
C. hostnamectl set-hostname Comptia-WebNode -H root@192.168.2.14
D. hostnamectl set-hostname Comptia-WebNode --transient
