AWS Certified Security - Specialty (SCS-C02): SCS-C02
Want to pass your AWS Certified Security - Specialty (SCS-C02) SCS-C02 exam in the very first attempt? Try Pass2lead! It is equally effective for both starters and IT professionals.
- Vendor: Amazon
- Exam Code: SCS-C02
- Exam Name: AWS Certified Security - Specialty (SCS-C02)
- Certifications: Amazon Certifications
- Total Questions: 851 Q&As( View Details)
- Updated on: May 28, 2026
- Note: Product instant download. Please sign in and click My account to download your product.

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
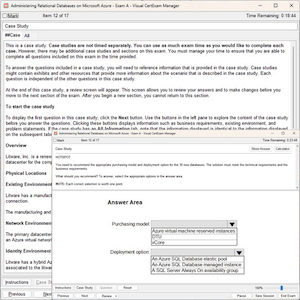
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
Passing Certification Exams Made Easy
Everything you need prepare and quickly pass the tough certification exams the first time
- 99.5% pass rate
- 7 Years experience
- 7000+ IT Exam Q&As
- 70000+ satisfied customers
- 365 days Free Update
- 3 days of preparation before your test
- 100% Safe shopping experience
- 24/7 Support
Amazon SCS-C02 Last Month Results
Free SCS-C02 Exam Questions in PDF Format
Related Amazon Certifications Exams
SCS-C02 Online Practice Questions and Answers
Questions 1
An organization has tens of applications deployed on thousands of Amazon EC2 instances. During testing, the Application team needs information to let them know whether the network access control lists (network ACLs) and security groups are working as expected.
How can the Application team's requirements be met?
A. Turn on VPC Flow Logs, send the logs to Amazon S3, and use Amazon Athena to query the logs.
B. Install an Amazon Inspector agent on each EC2 instance, send the logs to Amazon S3, and use Amazon EMR to query the logs.
C. Create an IAM Config rule for each network ACL and security group configuration, send the logs to Amazon S3, and use Amazon Athena to query the logs.
D. Turn on IAM CloudTrail, send the trails to Amazon S3, and use IAM Lambda to query the trails.
Questions 2
A security engineer receives a notice from the AWS Abuse team about suspicious activity from a Linux-based Amazon EC2 instance that uses Amazon Elastic Block Store (Amazon EBS>-based storage The instance is making connections to known malicious addresses
The instance is in a development account within a VPC that is in the us-east-1 Region The VPC contains an internet gateway and has a subnet in us-east-1a and us-easMb Each subnet is associate with a route table that uses the internet gateway as a default route Each subnet also uses the default network ACL The suspicious EC2 instance runs within the us-east-1 b subnet. During an initial investigation a security engineer discovers that the suspicious instance is the only instance that runs in the subnet
Which response will immediately mitigate the attack and help investigate the root cause?
A. Log in to the suspicious instance and use the netstat command to identify remote connections Use the IP addresses from these remote connections to create deny rules in the security group of the instance Install diagnostic tools on the instance for investigation Update the outbound network ACL for the subnet in us-east- lb to explicitly deny all connections as the first rule during the investigation of the instance
B. Update the outbound network ACL for the subnet in us-east-1b to explicitly deny all connections as the first rule Replace the security group with a new security group that allows connections only from a diagnostics security group Update the outbound network ACL for the us-east-1b subnet to remove the deny all rule Launch a new EC2 instance that has diagnostic tools Assign the new security group to the new EC2 instance Use the new EC2 instance to investigate the suspicious instance
C. Ensure that the Amazon Elastic Block Store (Amazon EBS) volumes that are attached to the suspicious EC2 instance will not delete upon termination Terminate the instance Launch a new EC2 instance in us-east-1a that has diagnostic tools Mount the EBS volumes from the terminated instance for investigation
D. Create an AWS WAF web ACL that denies traffic to and from the suspicious instance Attach the AWS WAF web ACL to the instance to mitigate the attack Log in to the instance and install diagnostic tools to investigate the instance
Questions 3
A security engineer is trying to use Amazon EC2 Image Builder to create an image of an EC2 instance. The security engineer has configured the pipeline to send logs to an Amazon S3 bucket. When the security engineer runs the pipeline, the build fails with the following error: "AccessDenied: Access Denied status code: 403".
The security engineer must resolve the error by implementing a solution that complies with best practices for least privilege access.
Which combination of steps will meet these requirements? (Choose two.)
A. Ensure that the following policies are attached to the IAM role that the security engineer is using: EC2InstanceProfileForImageBuilder, EC2InstanceProfileForImageBuilderECRContainerBuilds, and AmazonSSMManagedInstanceCore.
B. Ensure that the following policies are attached to the instance profile for the EC2 instance: EC2InstanceProfileForImageBuilder, EC2InstanceProfileForImageBuilderECRContainerBuilds, and AmazonSSMManagedInstanceCore.
C. Ensure that the AWSImageBuilderFullAccess policy is attached to the instance profile for the EC2 instance.
D. Ensure that the security engineer's IAM role has the s3:PutObject permission for the S3 bucket.
E. Ensure that the instance profile for the EC2 instance has the s3:PutObject permission for the S3 bucket.
Reviews
-
There are many new questions in the dumps and the answers are accurate and correct. I finished my exam with high score this morning, thanks very much.
-
Hello, guys. i have passed the exam successfully in the morning,thanks you very much.
-
when i seat for exam, i found that some answers are in different order in the real exam.so you can trust this dumps.
-
i cannot image that i would pass the exam with so high score, thanks for this dumps. Recommend.
-
Dump still valid, I got 979/1000 today. Thanks to you all.
-
Already pass. Valid dumps. Good site. Thanks guys.
-
Very useful study material, thanks the help of this dumps .
-
i'm an engineer and have not much time to prepare for the exam. Before two months, one of my friends intriduced this dumps to me. From then on, I only planned one hour to study this dumps and do the questions. Sometime i was so busy and had no time to do it. So before i begun my exam, I think I would fail the exam. But when i begun the exam, I found many same questions with the dumps, so i felt more and more confident and at last i passed the exam luckly. Thanks for this dumps and special to my friend.
-
Valid. Pass with 9XX. Good Luck!!!
-
Wonderful study material. I used this material only half a month, and eventually I passed the exam with high score. The answers are accurate and detailed. You can trust on it.

 Printable PDF
Printable PDF