EC-Council Certified Ethical Hacker (C|EH v12): 312-50V12
Want to pass your EC-Council Certified Ethical Hacker (C|EH v12) 312-50V12 exam in the very first attempt? Try Pass2lead! It is equally effective for both starters and IT professionals.
- Vendor: EC-COUNCIL
- Exam Code: 312-50V12
- Exam Name: EC-Council Certified Ethical Hacker (C|EH v12)
- Certifications: EC-COUNCIL Certifications
- Total Questions: 596 Q&As( View Details)
- Updated on: May 31, 2026
- Note: Product instant download. Please sign in and click My account to download your product.

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
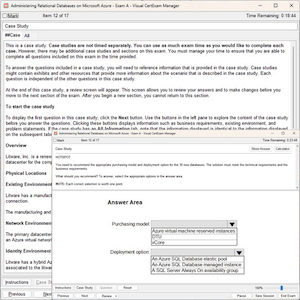
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
Passing Certification Exams Made Easy
Everything you need prepare and quickly pass the tough certification exams the first time
- 99.5% pass rate
- 7 Years experience
- 7000+ IT Exam Q&As
- 70000+ satisfied customers
- 365 days Free Update
- 3 days of preparation before your test
- 100% Safe shopping experience
- 24/7 Support
EC-COUNCIL 312-50V12 Last Month Results
Free 312-50V12 Exam Questions in PDF Format
Related EC-COUNCIL Certifications Exams
312-50V12 Online Practice Questions and Answers
Questions 1
An unauthorized individual enters a building following an employee through the employee entrance after the lunch rush. What type of breach has the individual just performed?
A. Reverse Social Engineering
B. Tailgating
C. Piggybacking
D. Announced
Questions 2
This TCP flag instructs the sending system to transmit all buffered data immediately.
A. SYN
B. RST
C. PSH
D. URG
E. FIN
Questions 3
Miley, a professional hacker, decided to attack a target organization's network. To perform the attack, she used a tool to send fake ARP messages over the target network to link her MAC address with the target system's IP address. By performing this, Miley received messages directed to the victim's MAC address and further used the tool to intercept, steal, modify, and block sensitive communication to the target system. What is the tool employed by Miley to perform the above attack?
A. Gobbler
B. KDerpNSpoof
C. BetterCAP
D. Wireshark
Reviews
-
I pass today, The dumps is good. 90% questions are from this dumps. so it is enough for the exam as long as you study this dumps carefully and do the all questions especially the new questions.
-
Paas my exam today. Valid dumps. Nice job!
-
Not take the exam yet. But i feel more and more confident with my exam by using this dumps. Now I am writing my exam on coming Saturday. I believe I will pass.
-
I studied this material carefully and took every question seriously. At last, I passed the exam with high score. Prepare well and study much more.
-
Very useful study material, thanks the help of this dumps .
-
Wonderful. I just passed,good luck to you.
-
the content update quickly, there are many new questions in this dumps. thanks very much.
-
Passed with unexpected score. A big surprise. Thanks very much.
-
The answers are accurate. Well you should notice some of the questions are slightly changed. Be careful.
-
Yes this valid. Passed today 982/1000. Same questions.

 Printable PDF
Printable PDF